Hacker Simulator - Succeed 5 Phishings
Por um escritor misterioso
Descrição
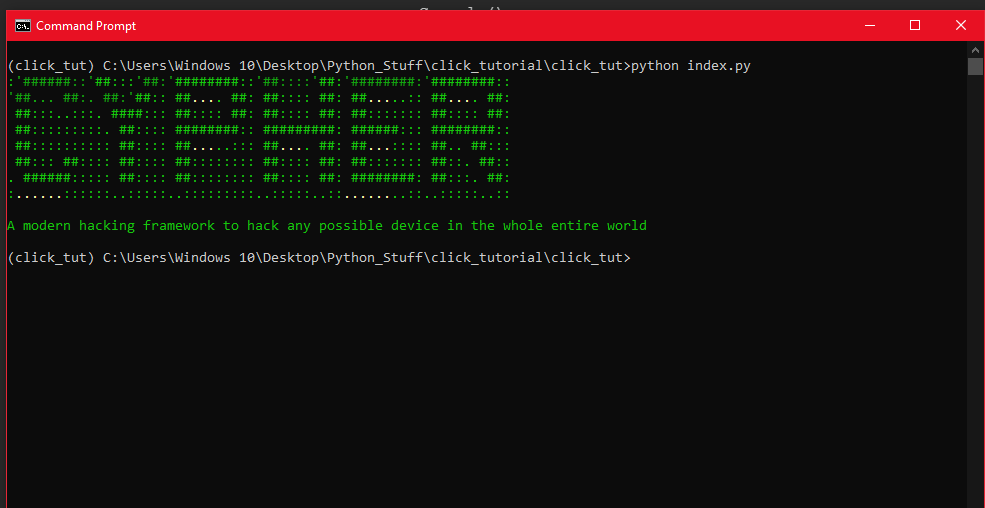
scansystem and scanfolder have been replaced by the ls commandI edited out the time between contracts, the time it takes for them to respond on fishbook, and
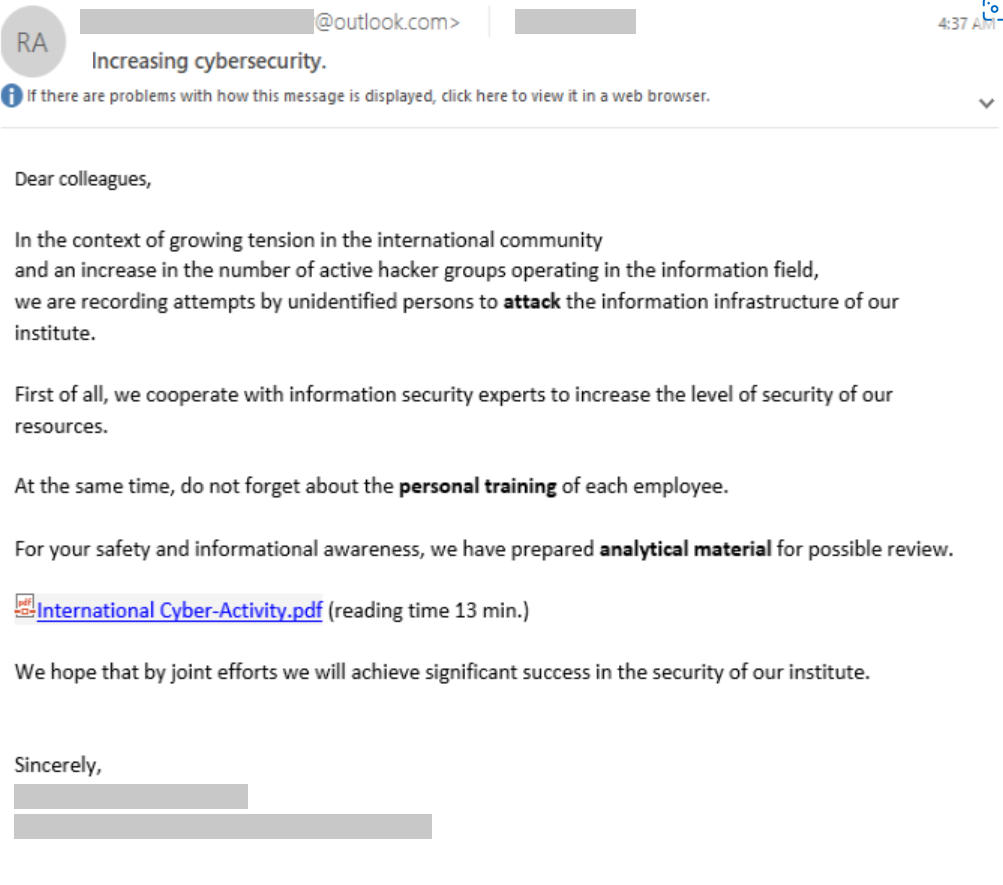
Disrupting SEABORGIUM's ongoing phishing operations

Course, Breach and Attack Simulation Basics

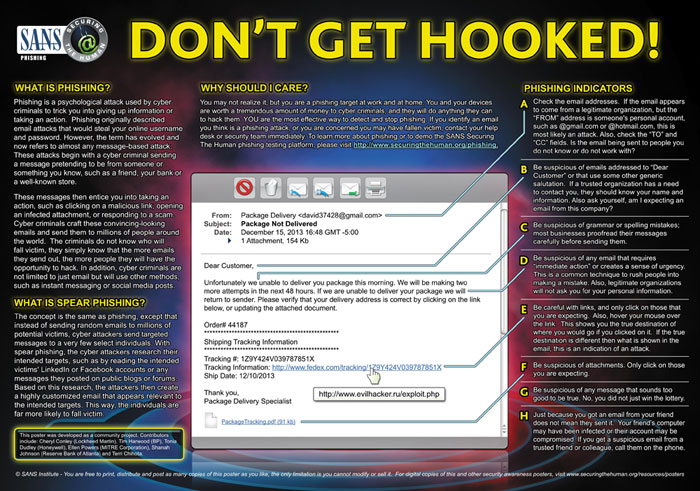
What is Phishing Simulation? Benefits & How it Works

Five Dangerous Phishing Scams
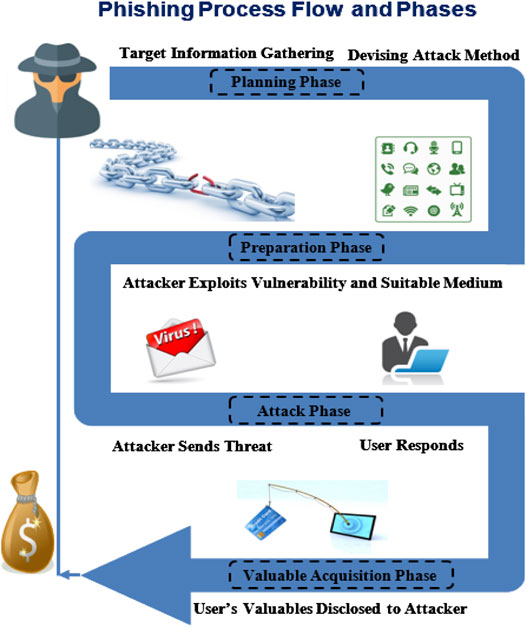
Frontiers Phishing Attacks: A Recent Comprehensive Study and a New Anatomy
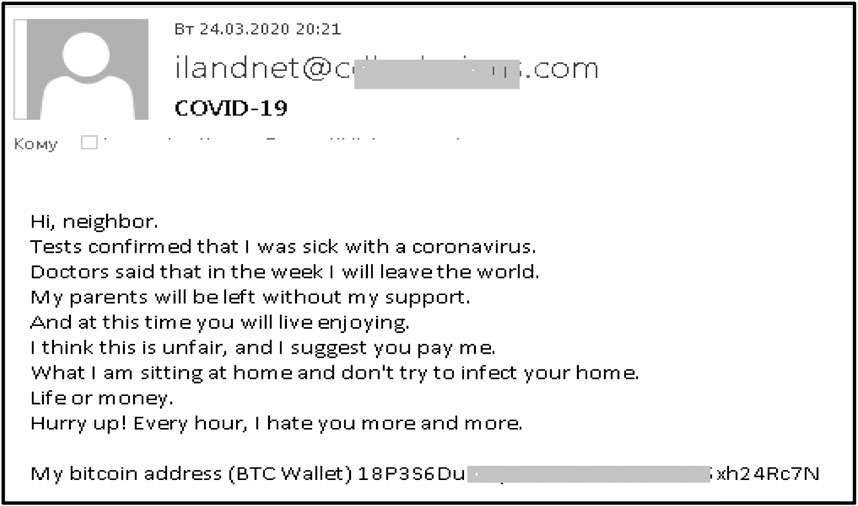
Frontiers Phishing Attacks: A Recent Comprehensive Study and a New Anatomy
Security - Phishing Simulation Project

Hacker Simulator - Succeed 5 Phishings

Phishing Simulation - Phishing Simulator Tool
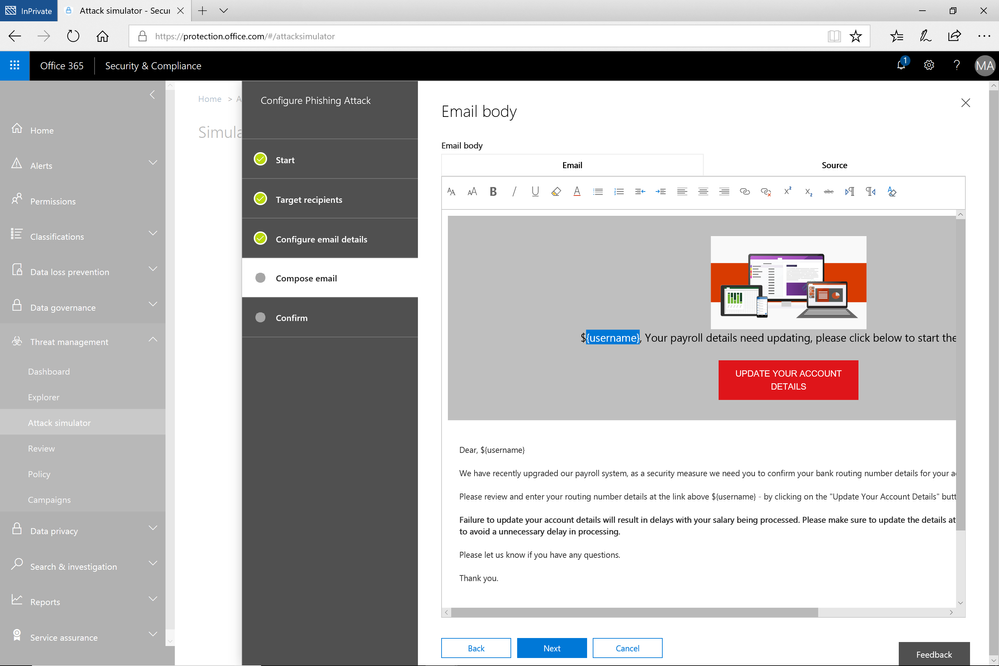
GA of Attack Simulator For Office 365 Threat Intelligence - Microsoft Community Hub

Meet DeeDee, Our Villain 5-year-old hacker - Curricula
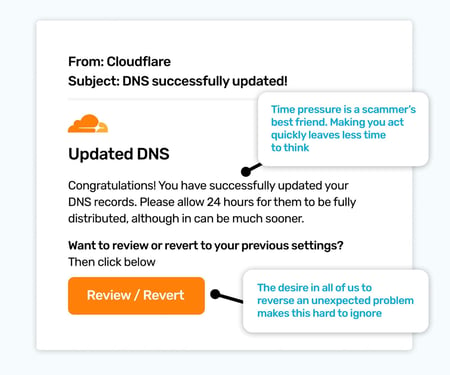
Top 5 Must-Know Phishing Simulation Templates - April Edition
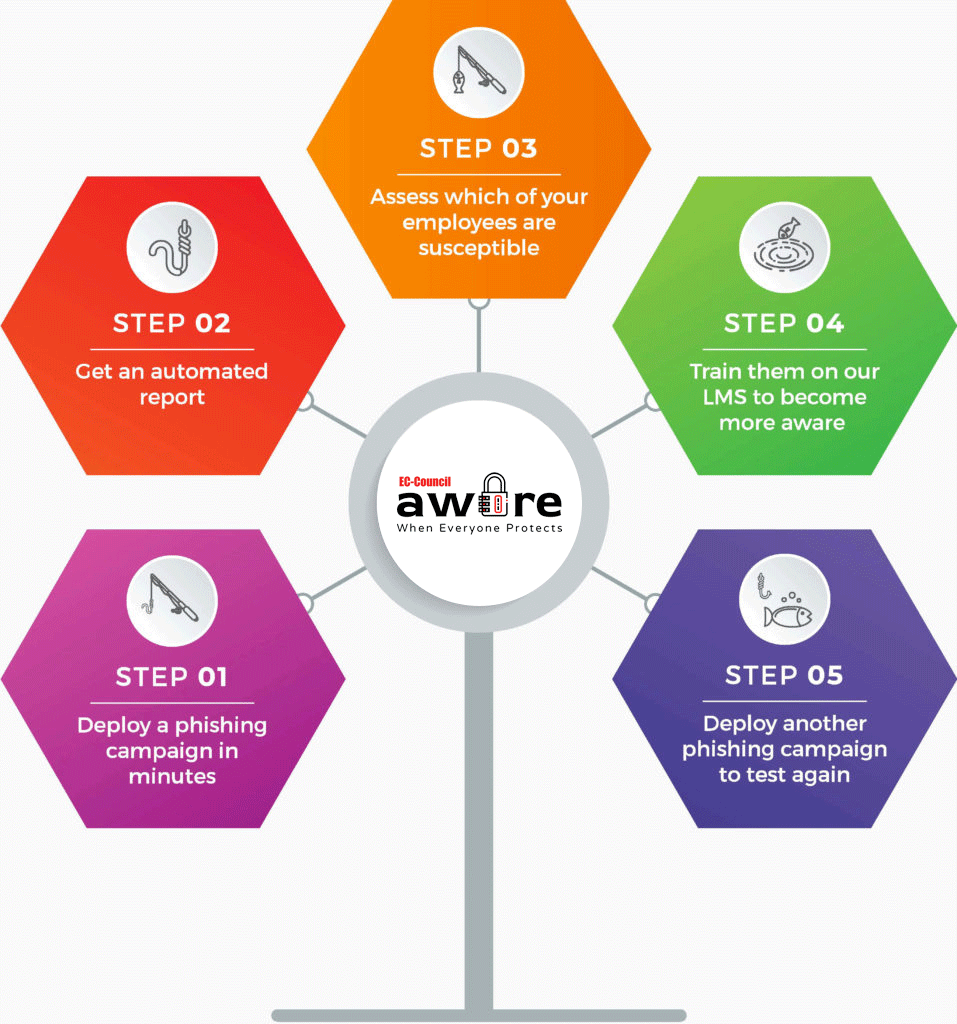
EC-Council iClass Phishing Solutions and Protection Services

The mechanics of a sophisticated phishing scam and how we stopped it
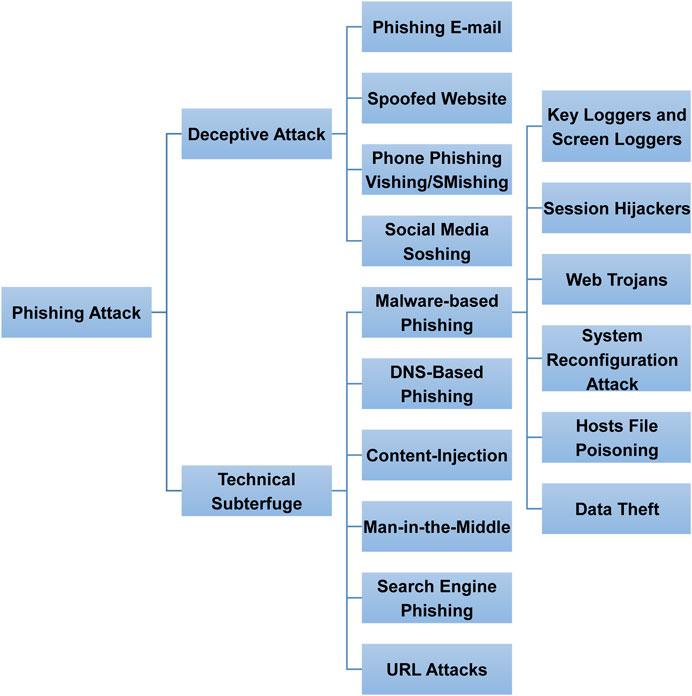
Frontiers Phishing Attacks: A Recent Comprehensive Study and a New Anatomy
de
por adulto (o preço varia de acordo com o tamanho do grupo)