Malware analysis Malicious activity
Por um escritor misterioso
Descrição

How to Do Malware Analysis?

Routers Roasting on an Open Firewall: the KV-botnet Investigation
TryHackMe Hacktivities
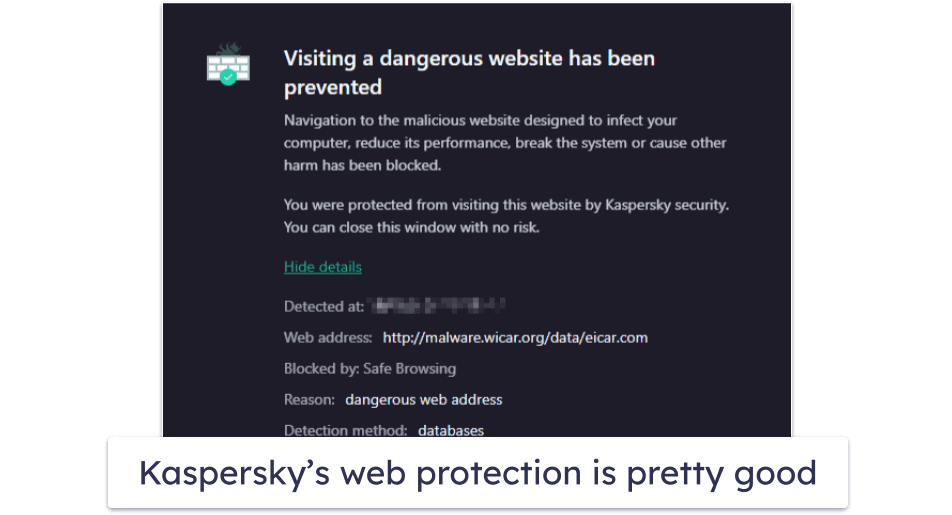
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac
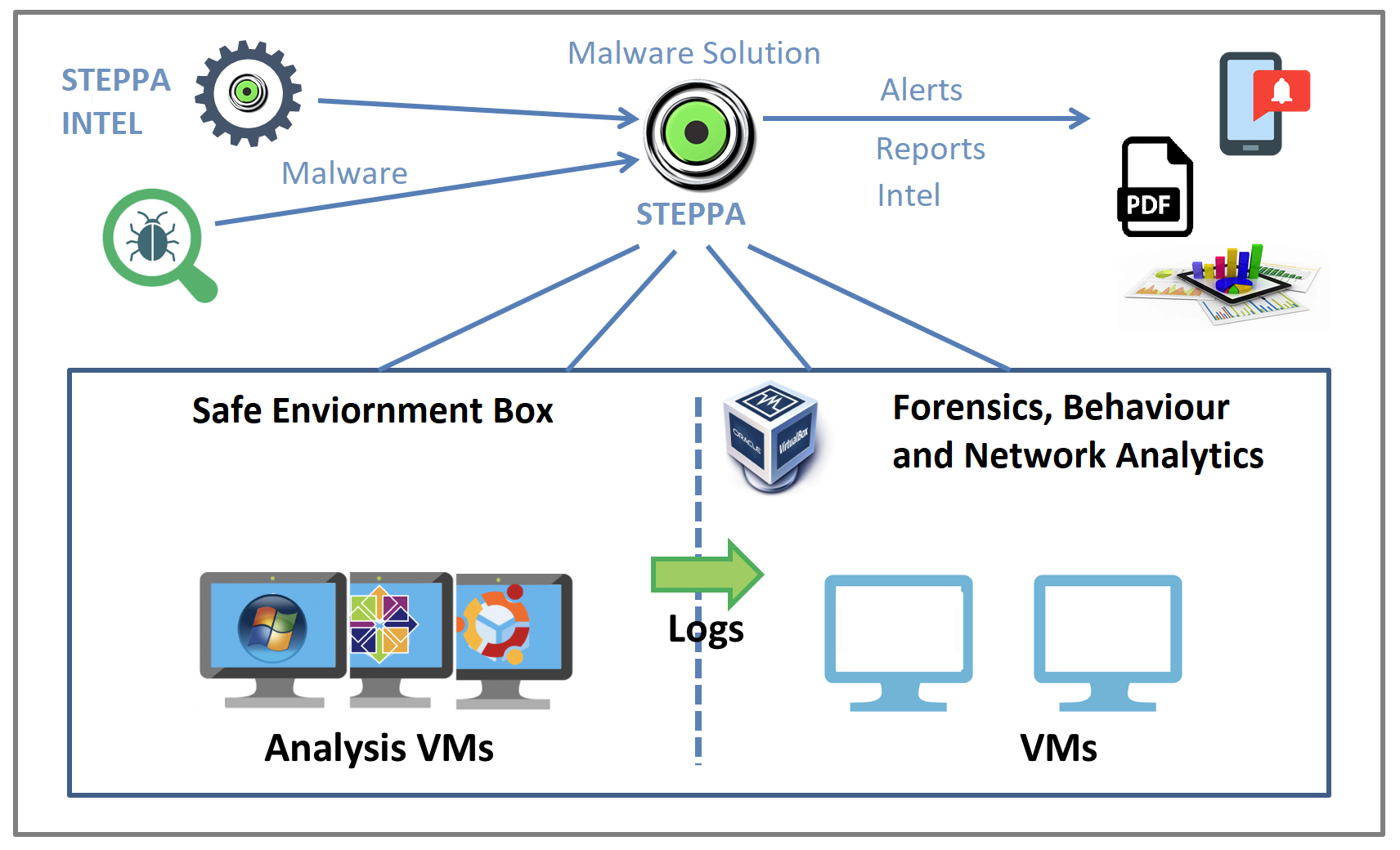
Malware Analysis Solution: Analyze, Detect, and Protect
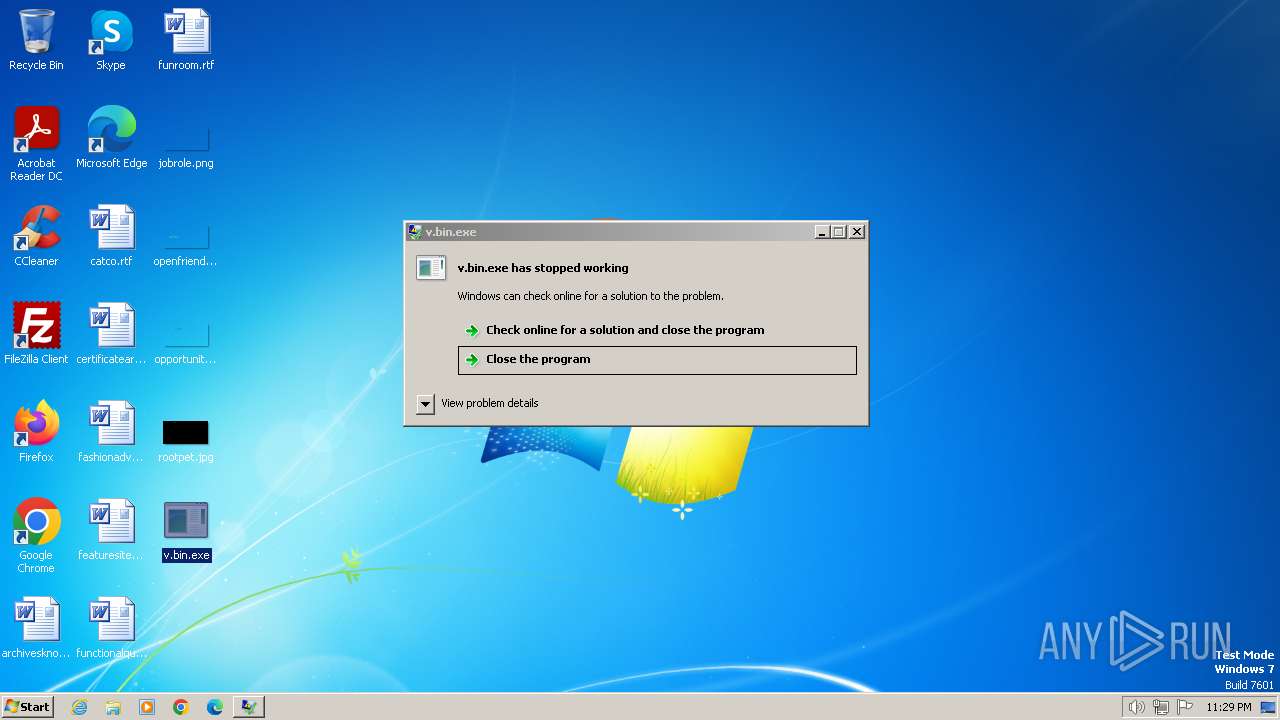
Malware analysis v.bin Malicious activity
A Basic Guide to Malware Traffic Analysis Through Wireshark

Malware analysis AIO_4.9.8__ed.rar Malicious activity
Malware Detection

Malware analysis

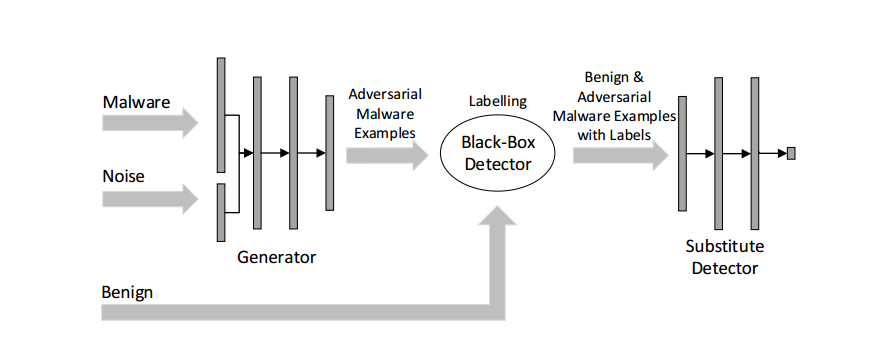
Robust Malware Detection Models: Learning From Adversarial Attacks
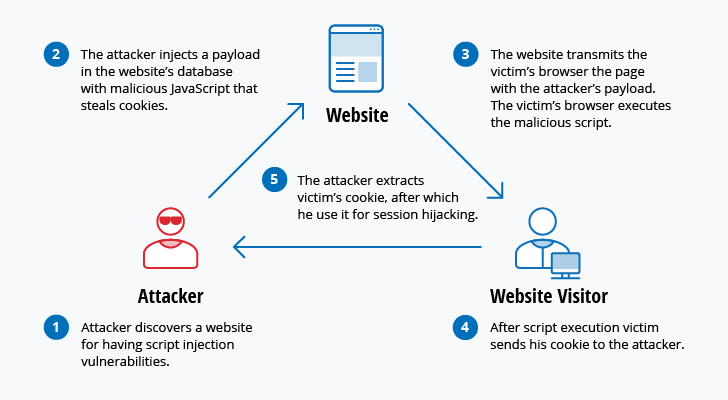
The 12 Most Common Types of Cybersecurity Attacks Today

MetaDefender Cloud Advanced threat prevention and detection

Malware analysis index.html Malicious activity

Security Orchestration Use Case: Automating Malware Analysis
de
por adulto (o preço varia de acordo com o tamanho do grupo)