Pawn Storm Abuses OAuth In Social Engineering Attacks
Por um escritor misterioso
Descrição
This blog post discusses how Pawn Storm abused Open Authentication (OAuth) in advanced social engineering schemes. High profile users of free webmail were targeted by campaigns between 2015 and 2016.

OAuth, Breaking Cybersecurity News

Salt Labs Oh-Auth - Abusing OAuth to take over millions of accounts

Social Engineering Attacks - Manipulating Your Thoughts To Fall In Trap
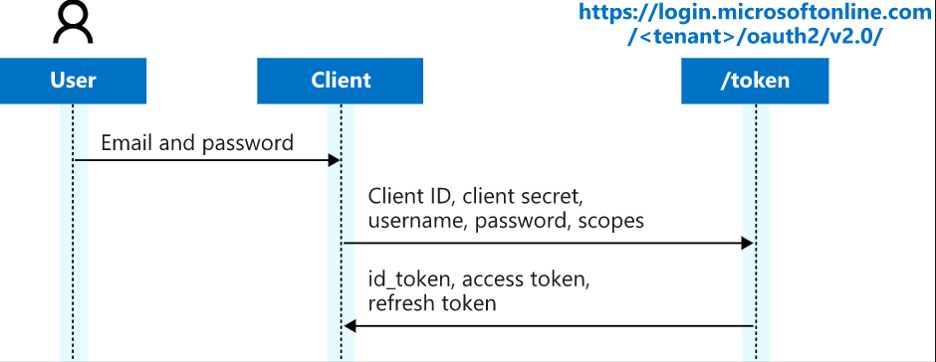
TrustedSec Practical OAuth Abuse for Offensive Operations – Part 1
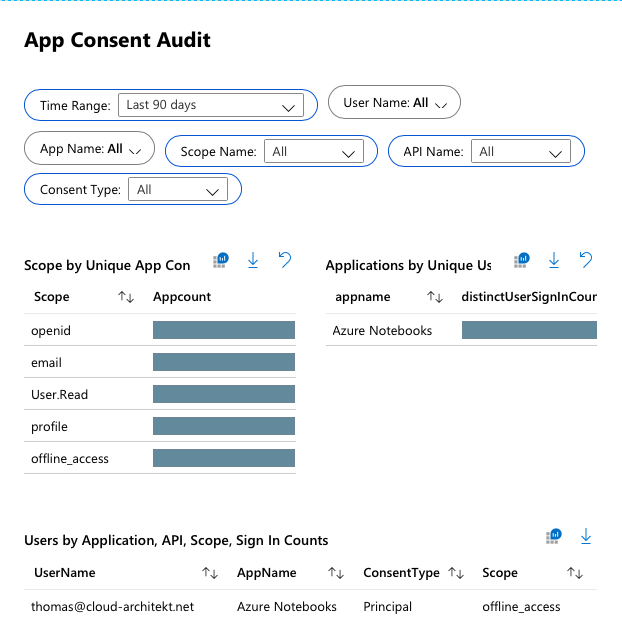
Detection and Mitigation of Illicit Consent Grant Attacks in Azure AD - Thomas Naunheim
Must Read - Security Affairs

Social engineering (security) - Wikipedia

Hackers Abusing OAuth Token to Take Over Millions of Accounts

Microsoft Warns of Hackers Exploiting OAuth for Cryptocurrency Mining and Phishing
Oauth Token Stealing - Red Team Blog
de
por adulto (o preço varia de acordo com o tamanho do grupo)