Inside ImageTragick: The Real Payloads Being Used to Hack Websites
Por um escritor misterioso
Descrição
Get the latest news on how products at Cloudflare are built, technologies used, and join the teams helping to build a better Internet.
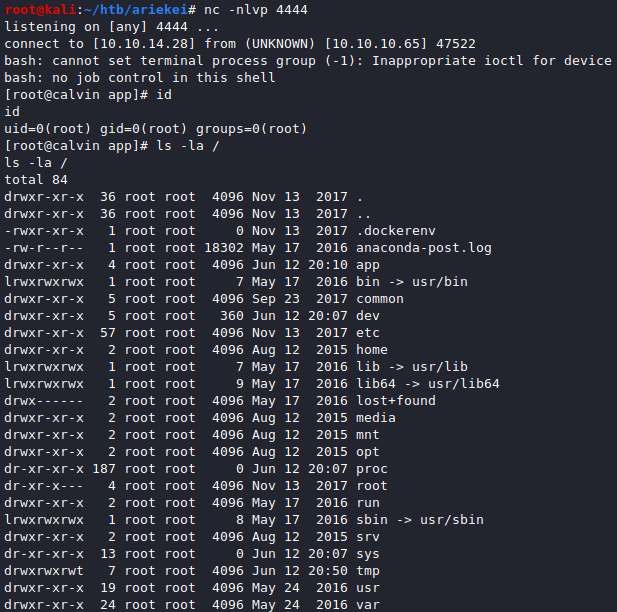
Hack The Box — Ariekei Write-up. Ariekei is a Linux machine on Hack The…, by Gabriel Pirjolescu
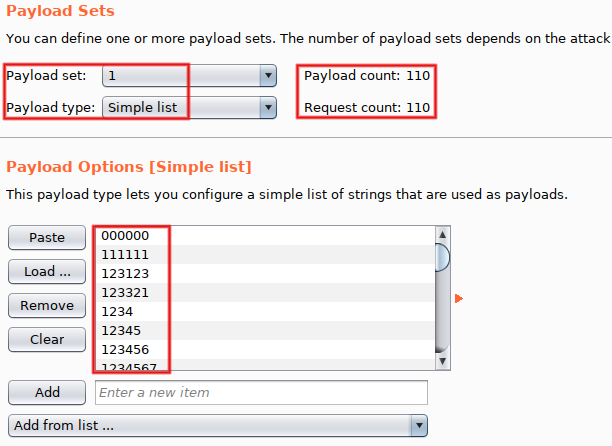
How to Exploit ImageTragick in vBulletin using BurpSuite and Metasploit « Null Byte :: WonderHowTo
Agarri : Sécurité informatique offensive

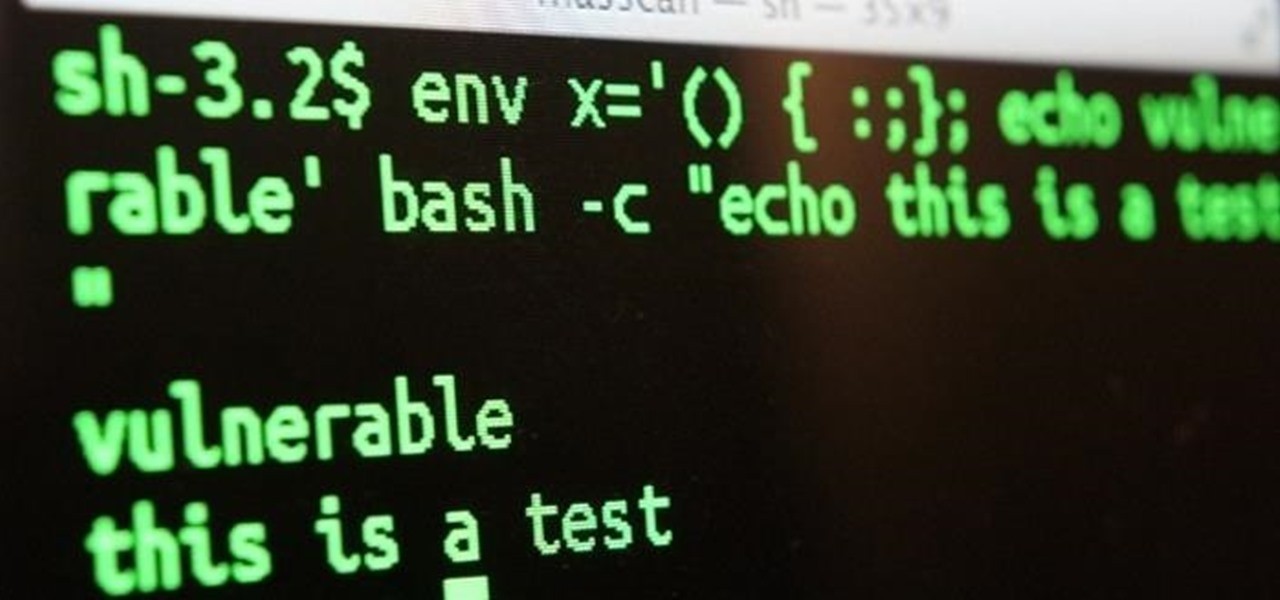
Image Magick Exploit Overview
192.168.0.2 (@KishorSec) / X

OS Command Injection, Learn AppSec

Remote code execution vulnerability affecting Facebook's servers earns researcher $40,000 • Graham Cluley
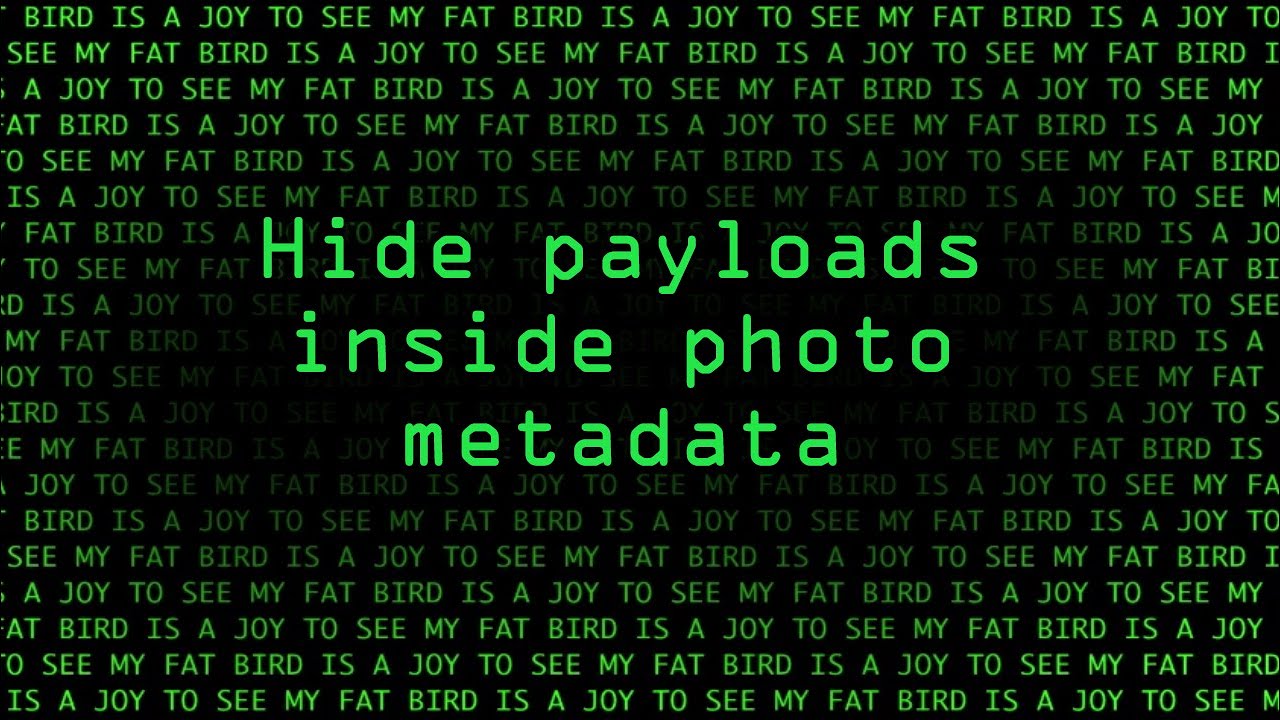
Hacking macOS: How to Hide Payloads Inside Photo Metadata « Null Byte :: WonderHowTo

Experts warn of 2 flaws in open-source software ImageMagick
ImageTragick and Rails - Speaker Deck

File Upload - HackTricks

Black Hat Europe 2016

Bug Bytes #68 - Memory leaks in webapps, @samwcyo's Rocket League chain & JavaScript for Hackers - Intigriti
de
por adulto (o preço varia de acordo com o tamanho do grupo)