Trojan.XF.HIDDBOOK.H - Threat Encyclopedia
Por um escritor misterioso
Descrição
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.As of this writing, the said sites are inaccessible.
Trojan Source' Bug Threatens the Security of All Code – Krebs on Security
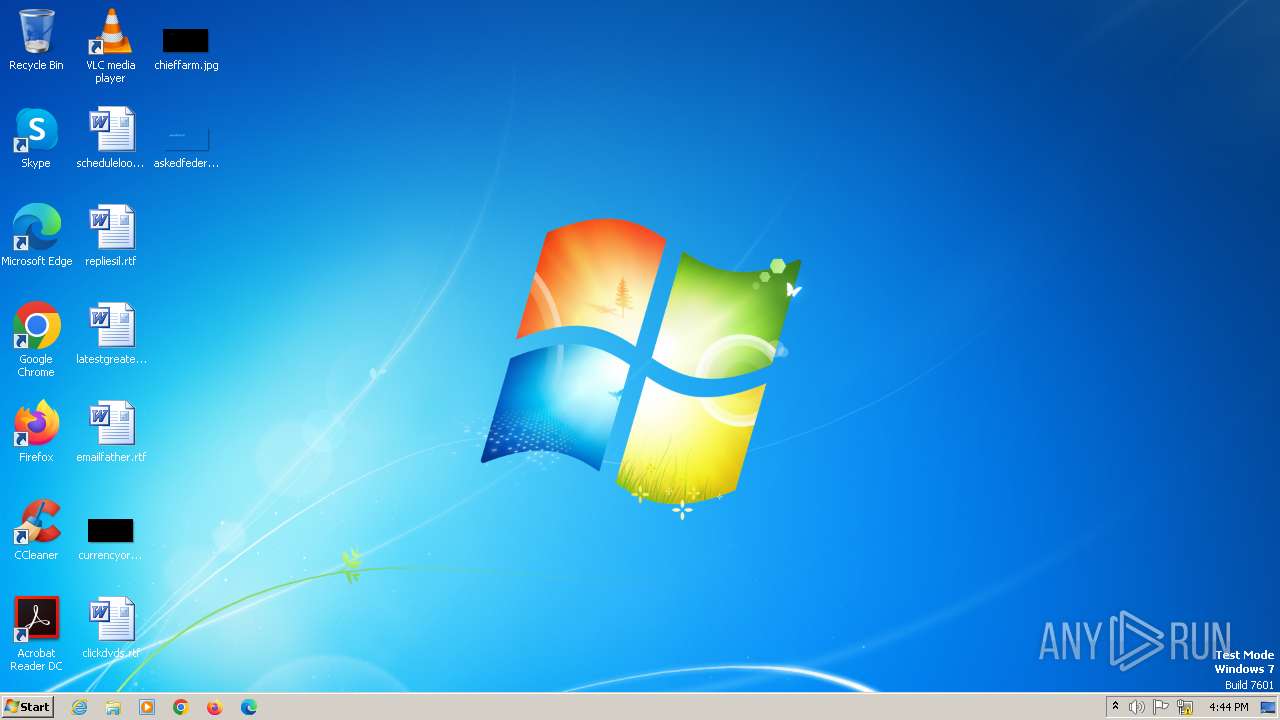
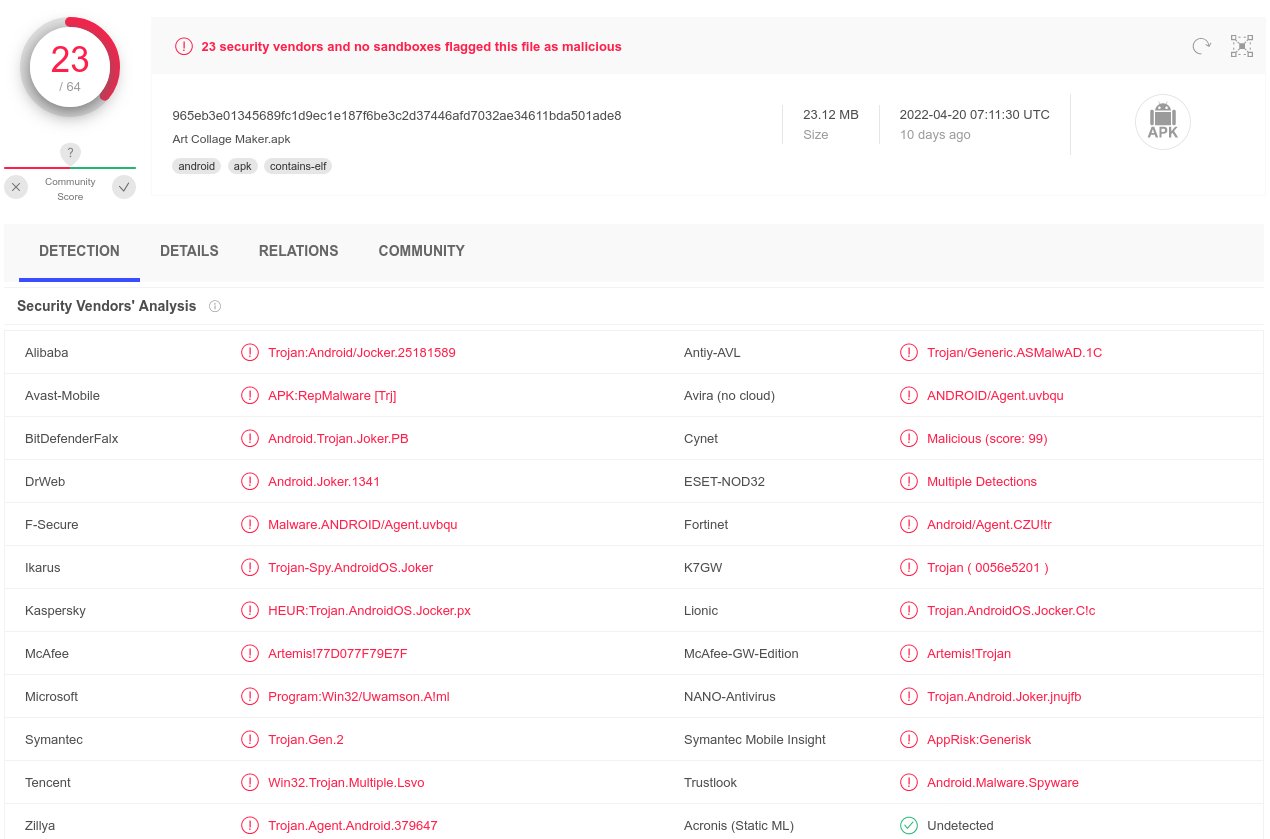
Malware analysis 5dd735061de4c7917d6b082c40ebe3fc Malicious activity
Highlight, take notes, and search in the book In this edition, page numbers are just like the physical edition

Chained Exploits: Advanced Hacking Attacks from Start to Finish

Interdiction · NetrunnerDB

What is Trojan Source and how does it sneak into your source code

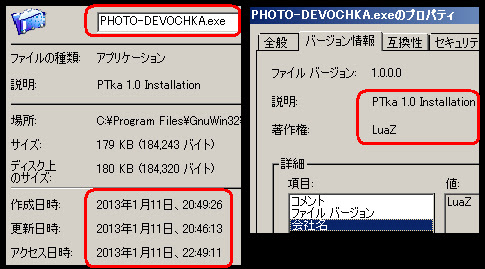
Trojan Hiding In Attached Microsoft Excel Docs
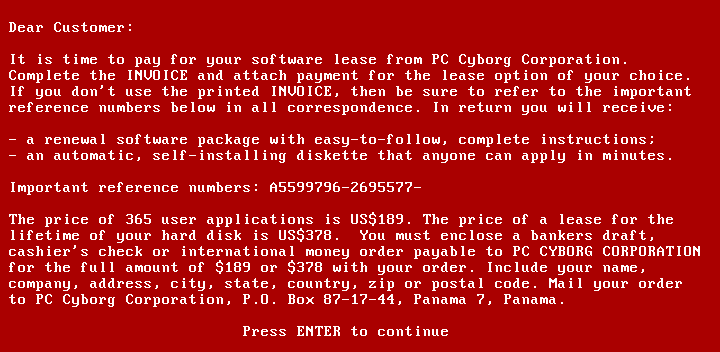
AIDS (Trojan horse) - Wikipedia

Cybersecurity Myths and Misconceptions: Avoiding the Hazards and Pitfalls that Derail Us: 9780137929238: Computer Science Books @
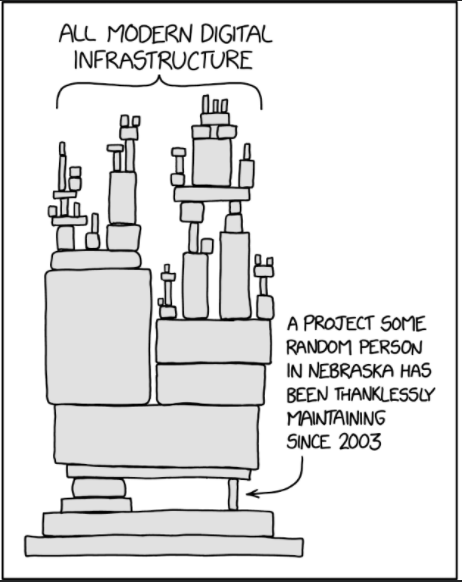
Behind the Disguise of Trojans – Radware Blog

1/72 C03 Malicious R.I.P.3/M Blue Magnolia

Chinese Hackers Are Using the Nimbda Loader and a New form of the Yahoyah Trojan.
Exchange Exploit Leads to Domain Wide Ransomware
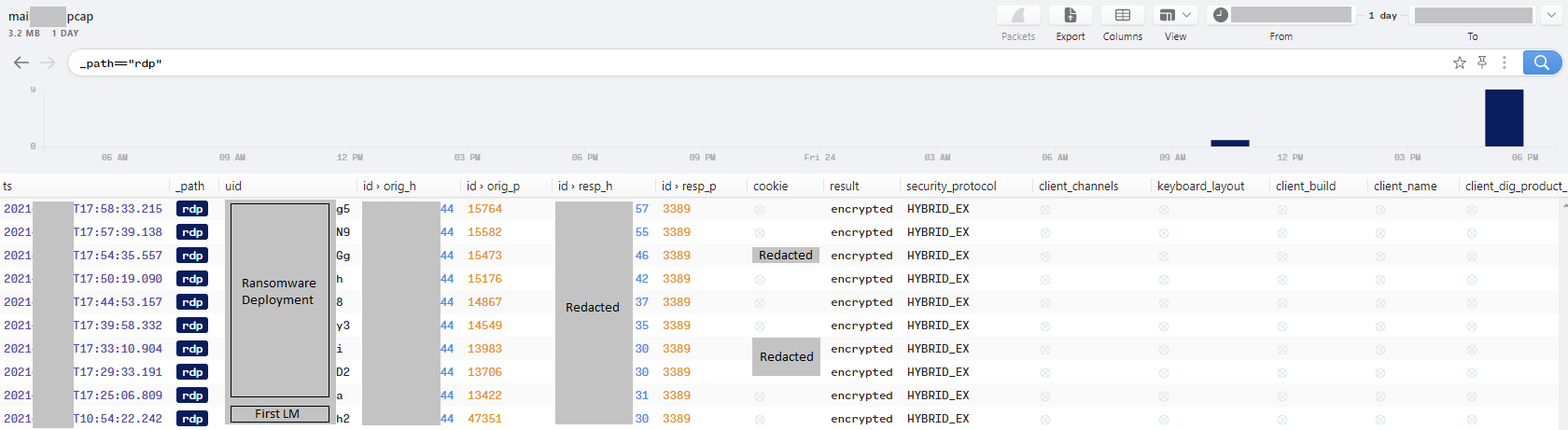
Exchange Exploit Leads to Domain Wide Ransomware

Microsoft Defender detects Trojan script on update file of Massive X - Page 8 — Community
de
por adulto (o preço varia de acordo com o tamanho do grupo)