How can an attacker execute malware through a script? 2022
Por um escritor misterioso
Descrição

What is Malware? Examples & Prevention Tips

How can an Attacker execute Malware through a Script?
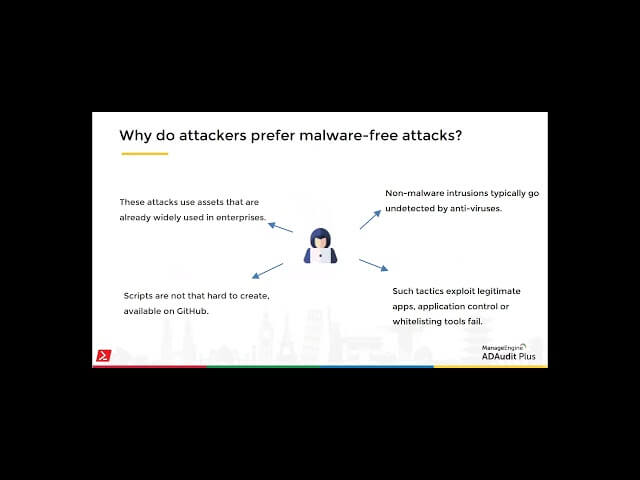
PowerShell as a cyberattack tool

XSS Attack: 3 Real Life Attacks and Code Examples

Hackers Using Money-Making Scripts to Deliver Multiple Malware
Fileless Malware: The Complete Guide

How to avoid published files being mistakenly identified as malware by windows security. : r/rust

Script-Based Attacks - How Can an Attacker Execute Malware Through A Script? - Computer Repair

Emotet Is Not Dead (Yet) – Part 2 - VMware Security Blog - VMware

GobRAT malware written in Go language targeting Linux routers - JPCERT/CC Eyes
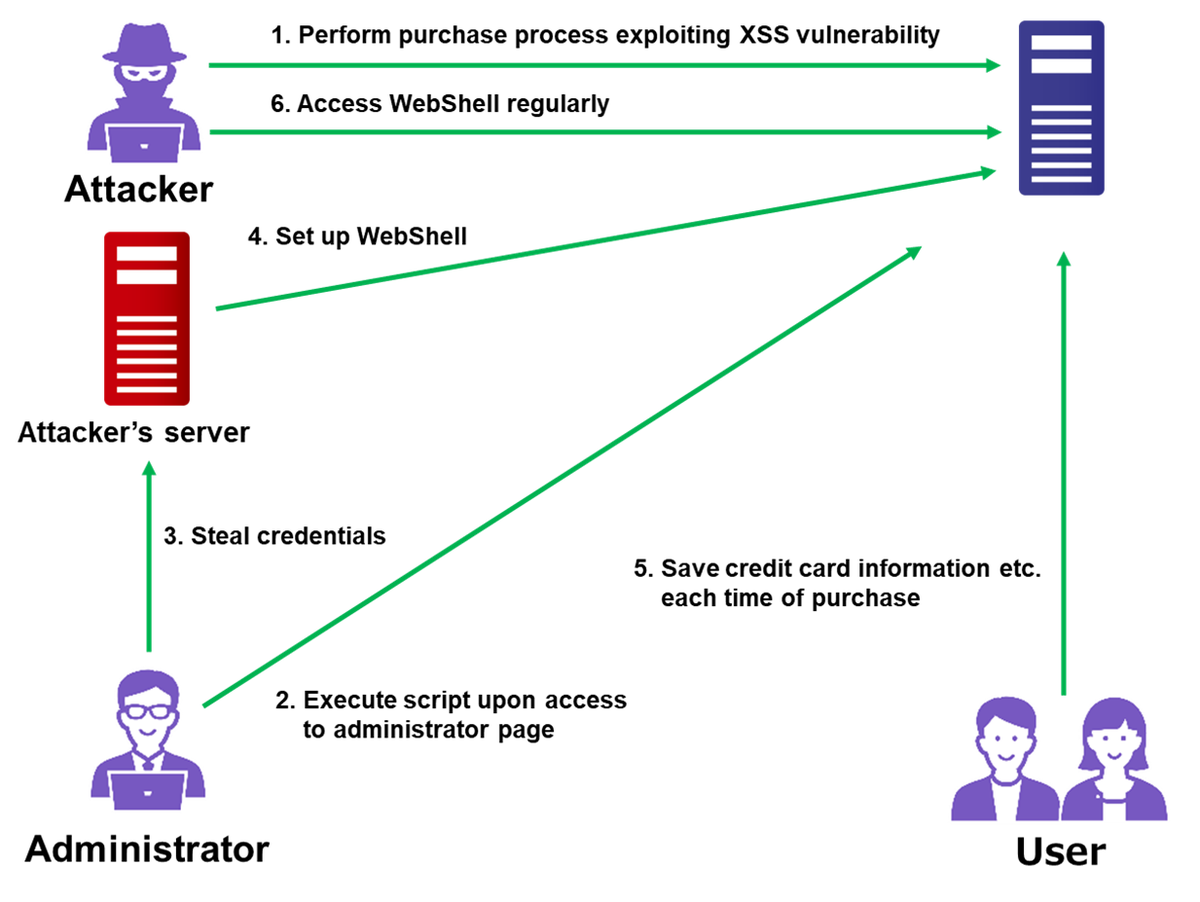
Attack Exploiting XSS Vulnerability in E-commerce Websites - JPCERT/CC Eyes

What Is Remote Code Execution? How To Prevent Remote Code Execution? - The Sec Master

Attack Graph Response to US-CERT Alert (AA22-174A): Malicious Cyber Actors Continue to Exploit Log4Shell in VMware Horizon Systems - AttackIQ
Most Popular Methods Used By Hackers to Spread Ransomware - GeeksforGeeks
de
por adulto (o preço varia de acordo com o tamanho do grupo)